A customer of ours asked us to look into making their environment more secure.
We did some penetration testing against their domain and found a few things to adjust.
However we noticed that they did not audit Group/User changes in their Active Directory, we adjusted this and here’s a quick guide how to deploy it in your corporation (this guide is for Windows Server 2008 and later).
First of all go to the Group Policy Management console.
Expand down to Group Policy Objects and create a new policy called Domain Auditing.
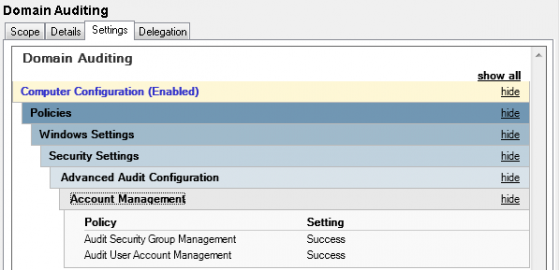
Edit the policy and browse down to the correct setting:
Computer Configuration > Policies > Windows Settings > Security Settings > Advanced Audit Configuration > Audit Policies > Account Management
I usually just enable Security Group and User Account changes, since those are the most common and most likely to be what you will be looking for. However there are way more auditing settings available.
Check the Configure the following audit events, and then select Success. Press OK and close the editor.
Now the last step is to link the GPO to your Domain Controller OU, and verify that Security Filtering is set to “Authenticated Users” or “Domain Controllers” (preferred).
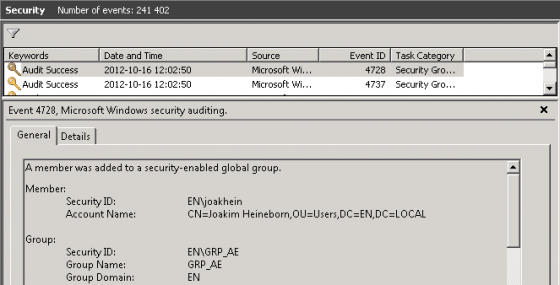
When that is done make a change to a group and verify that the Domain Controller is logging the events, if everything is correct it should look something like this:
Event ID / Action
4720 : A user account was created.
4722 : A user account was enabled.
4723 : An attempt was made to change an account’s password.
4724 : An attempt was made to reset an account’s password.
4725 : A user account was disabled.
4726 : A user account was deleted.
4738 : A user account was changed.
4740 : A user account was locked out.
4765 : SID History was added to an account.
4766 : An attempt to add SID History to an account failed.
4767 : A user account was unlocked.
4780 : The ACL was set on accounts which are members of administrators groups.
4781 : The name of an account was changed:
4794 : An attempt was made to set the Directory Services Restore Mode.
5376 : Credential Manager credentials were backed up.
5377 : Credential Manager credentials were restored from a backup.
4727 : A security-enabled global group was created.
4728 : A member was added to a security-enabled global group.
4729 : A member was removed from a security-enabled global group.
4730 : A security-enabled global group was deleted.
4731 : A security-enabled local group was created.
4732 : A member was added to a security-enabled local group.
4733 : A member was removed from a security-enabled local group.
4734 : A security-enabled local group was deleted.
4735 : A security-enabled local group was changed.
4737 : A security-enabled global group was changed.
4754 : A security-enabled universal group was created.
4755 : A security-enabled universal group was changed.
4756 : A member was added to a security-enabled universal group.
4757 : A member was removed from a security-enabled universal group.
4758 : A security-enabled universal group was deleted.
4764 : A group’s type was changed.
If this helped you, or if you’re having issues feel free to stop a line below.

Very informative !
Due to lack of time, I use an automated solution from Lepide i.e., (http://www.lepide.com/active-directory-audit/) that is very useful to audit active directory users account activities in my organization. It notify of all critical changes made at granular level by sending customized email notification (whether someone changed policy, created new user account, enabled/disabled or deleted some users in active directory.
Thanks for sharing such this valuable information.
I have also checked this article ( http://www.esystool.com/how-to-enable-active-directory-security-auditing/ ) audit the changes made in my active directory environment. It provides an appropriate solution for auditing all the critical changes at granular level and provide the report with real time monitoring.
However, this well described article looks a good start-up in my future reference while need to monitor AD environment.