Welcome to the Jocha blog!
Enroll in Azure AD with error 8018000a
The 801800A issue is usually caused by a Windows client thinking it has a enrollment to Azure AD in progress. It will not “time out” so you will have to manually fix this…
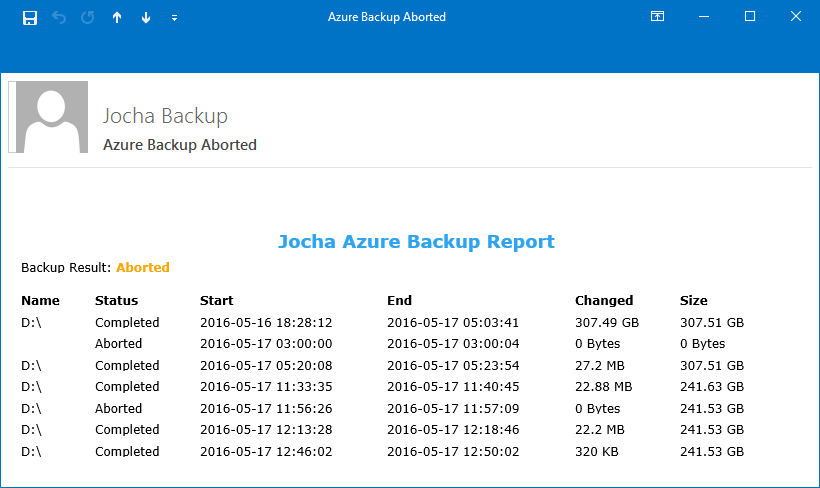
Office365 Safe Attachment Delay Report
Recently the Helpdesk have been getting cases about slow delivery times due to Office 365 ATP Safe Attachments. We have created a script to retrieve the data from Exchange Online, and then used Power BI to visualize it.
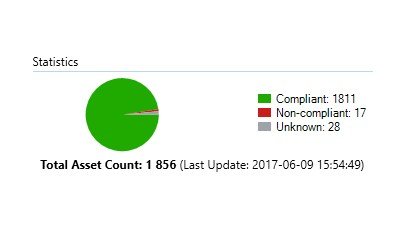
SCCM Baselines: Update Compliance
There are numerous of ways to measure update compliance in an enterprise. Some prefer to just compare the compliance of a Software Update Group against a collection. The issue I’ve found with this is that when you release updates the compliance falls down to 0%…
SCCM Baselines: Intrusion and Theft Protection
This article focuses on the scenario where the laptop/desktop has been lost or stolen, and how to make sure that the local data/credentials are secured/encrypted.
Resetting Password for Specific OU
I created a powershell-script which will reset the password of all users in a specific Organizational Unit.
I prefer to set unique high-end passwords for all users. If you prefer a more ‘user friendly’ approach simply…
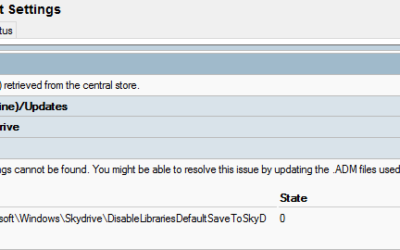
Remove Orphaned ADMX GPO values
A downside with the ADMX files is that when you update them, and the new files replace settings and values you end up with orphaned settings in your GPOs. In our example we had two orphaned registry values from a previous OneDrive ADMX.
Disable Windows 10 Automatic locking screen
We’ve been upgrading a customers environment… for one of their workstation configurations they didn’t want the computers to lock on idle, which is enforced by default.
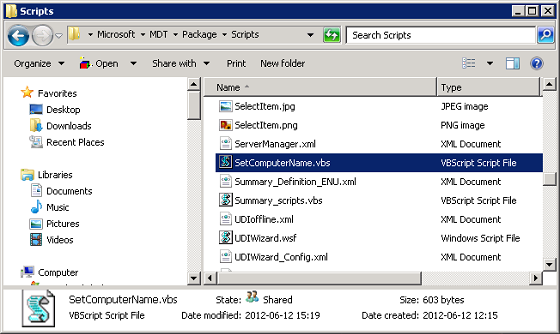
MDT 2013 Set Computername with VBS
Back in 2012 I wrote an article about dynamically setting a computer name during a Task Sequence. Here is my updated and improved script. I’m currently setting up a deployment solution running SCCM with MDT 2013…