Onboarding devices to Microsoft Defender for Endpoint individually through the Security Center is time-consuming and difficult to track at scale. Using PowerShell and the Microsoft Graph Security API, you can automate onboarding, verify sensor health, and generate...
Security
Configuring Conditional Access Policies with Microsoft Entra ID
Conditional Access is the cornerstone of Zero Trust security in Microsoft Entra ID. Rather than managing dozens of policies by hand through the Azure portal, you can use PowerShell and the Microsoft Graph API to define, deploy, and version-control your policies with...
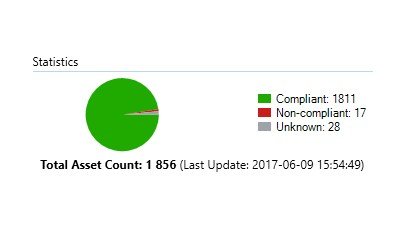
SCCM Baselines: Update Compliance
There are numerous of ways to measure update compliance in an enterprise. Some prefer to just compare the compliance of a Software Update Group against a collection. The issue I’ve found with this is that when you release updates the compliance falls down to 0%…
SCCM Baselines: Intrusion and Theft Protection
This article focuses on the scenario where the laptop/desktop has been lost or stolen, and how to make sure that the local data/credentials are secured/encrypted.
Resetting Password for Specific OU
I created a powershell-script which will reset the password of all users in a specific Organizational Unit.
I prefer to set unique high-end passwords for all users. If you prefer a more ‘user friendly’ approach simply…
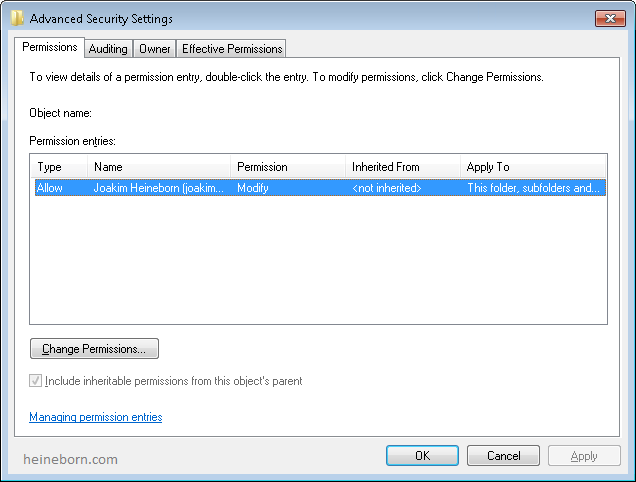
Fix Users Homefolder Permissions
The script will look through the a selected Organization Unit and verify that all users have a Home Directory set, and that it has the appropriate NTFS permissions.
Previously all users had Full-permissions on their home folder, which led to the users resetting permissions and removing unwanted permissions (Backup or Admin accounts) to their “private” stuff.
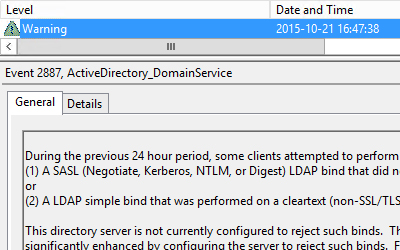
SASL/LDAP Simple warning on Domain Controllers
I noticed that a couple of Domain Controllers started reporting Warning-messages. It turns out that one or more clients have been using LDAP binds that are performed on a clear text (non-SSL/TLS-encrypted) connection.
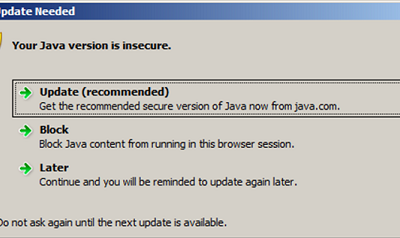
Uninstall all Java versions
I received an inquiry from one of my mid-size (100-200 users) customers today. They’ve been planning on implementing a new online service which requires the latest Java version.
The clients have a large quantity of outdated versions of Java, which needed to be uninstalled before we deployed the newest version.
They are currently running Windows 7 and Windows 8, so somewhat modern operative systems.
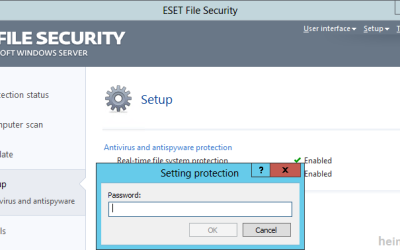
Resetting or clearing NOD32 client password
I was faced with an issue regarding NOD32 today. A couple of clients had an old (undocumented) configuration of their antivirus.
As it turned out the clients had “Protected setup” which means you cannot access the settings, or un/reinstall the program without a specific password. It also happened to not be set up to talk to the appropriate “Remote Administrations-server”.
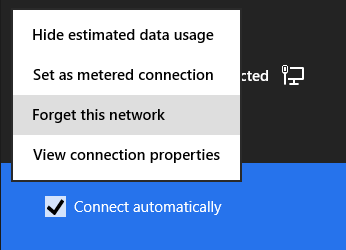
Display all saved WiFi Passwords
We’ve all been there, wireless passwords tend get lost.
There are several tools to retrieve the missing information, but I strongly believe that the less stuff you download from the web, the safer you are. So why not use the built in functions instead?