Windows Autopilot transforms device provisioning from a multi-hour imaging process into a zero-touch deployment experience. When you combine it with PowerShell automation, you can register hardware hashes, assign profiles, and track enrollment status entirely from the...
PowerShell
Automating Intune Device Compliance Policies with PowerShell
Manually configuring Microsoft Intune compliance policies across hundreds of devices is tedious and error-prone. By leveraging the Microsoft Graph API through PowerShell, you can define, deploy, and audit compliance policies programmatically — making your...
Office365 Safe Attachment Delay Report
Recently the Helpdesk have been getting cases about slow delivery times due to Office 365 ATP Safe Attachments. We have created a script to retrieve the data from Exchange Online, and then used Power BI to visualize it.
SCCM Baselines: Intrusion and Theft Protection
This article focuses on the scenario where the laptop/desktop has been lost or stolen, and how to make sure that the local data/credentials are secured/encrypted.
Resetting Password for Specific OU
I created a powershell-script which will reset the password of all users in a specific Organizational Unit.
I prefer to set unique high-end passwords for all users. If you prefer a more ‘user friendly’ approach simply…
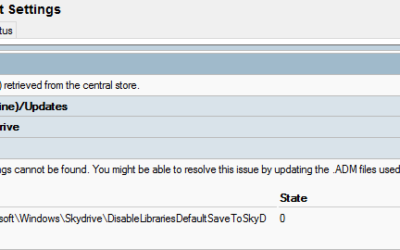
Remove Orphaned ADMX GPO values
A downside with the ADMX files is that when you update them, and the new files replace settings and values you end up with orphaned settings in your GPOs. In our example we had two orphaned registry values from a previous OneDrive ADMX.
Remove App Packages in Windows 10 1607
There are a few different approaches when it comes to cleaning up the Windows 10 deployment. I prefer to uninstall the built-in applications which my enterprise and customers have no need for.
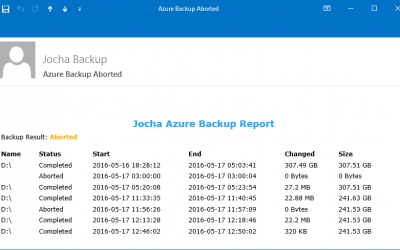
Azure Backup Mail Report Script
Jocha previously released a very popular mail report-script for Windows Backup. A downside with the new Azure backup-agent is that it did not offer mail reports… until today!
Detect and Elevate a PowerShell session
We’ve set out to help a customer with automation within their IT department.
Some daily tasks require an elevated prompt, there is no way around it. But it’s not obvious how to check if the current prompt is elevated, or how to elevate the session. So here is a how-to…
PowerShell: Get-WMIComputerSessions
This PowerShell-script retrieves all current user sessions on a local or remote system.